Proactive Cybersecurity &
IT Management
You shouldn’t have to worry about your software updates failing, your company server being hacked, or whatever the latest cybersecurity regulations are. At A&B, we provide comprehensive, state-of-the-art IT solutions tailored to your business. Let us partner with your IT team-or be your IT team-and monitor your environment so you don’t lose data or experience cyberattacks.
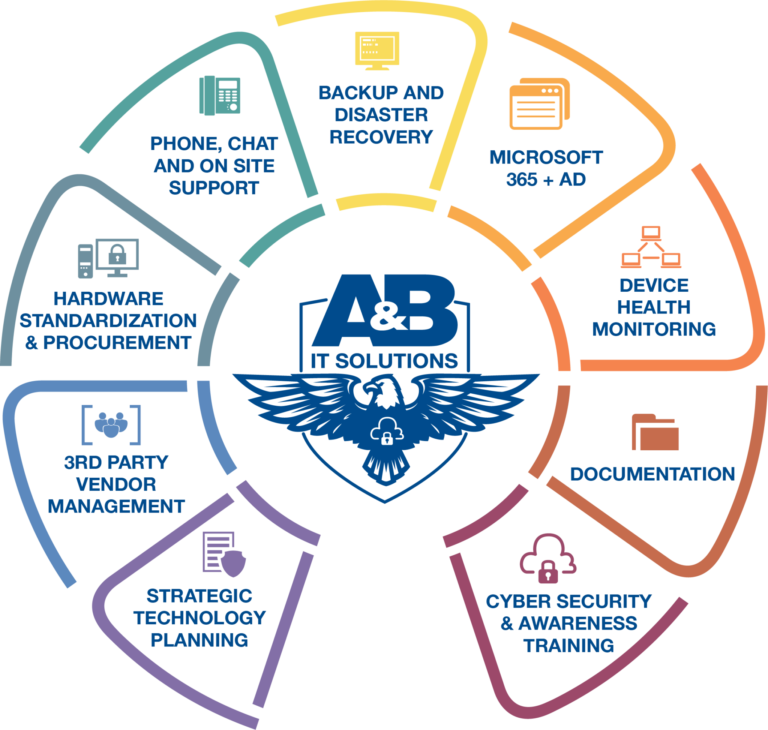
Developing long-term strategies so your IT plan aligns with your business goals.
Overseeing and coordinating relationships with external service providers to ensure quality and compliance.
Establishing consistent hardware standards and managing equipment acquisition.
Providing technical assistance through various channels, including phone, online chat, and in-person visits.
Implementing systems to regularly backup and restore data in case of data loss or emergencies.
Overseeing and coordinating relationships with external service providers to ensure quality and compliance.
Tracking the performance and health of devices to prevent issues and maintain efficiency.
Creating and maintaining detailed records of processes, systems, and procedures for reference and compliance.
Educating Employees on best practices for protecting information and systems from cyber threats.
Strategic Technology Planning
Strategic Technology Planning
3rd Party Vendor Management
3rd Party Vendor Management
Hardware Standardization & Procurement
Hardware Standardization & Procurement
Phone, Chat, & On-Site Support
Phone, Chat, & On-Site Support
Backup & Disaster Recovery
Backup & Disaster Recovery
Microsoft 365 & Active Directory
Microsoft 365 & Active Directory
Device Health Monitoring
Device Health Monitoring
Documentation
Documentation
Cyber Security & Awareness Training
Cyber Security & Awareness Training
Get a Risk Assessment
Request a Quote
How does A&B IT management work?
We know IT and cybersecurity aren't one-size-fits-all things, so our specialists evaluate your environment and help you choose the best plan for your needs and budget. Then you can hand your IT worries over to us, and we'll take care of them.
Why Choose A&B?
- Straightforward support agreements
- Great customer experience
- Customized support plans
- Respond to issues within hours, not weeks
Security can be difficult to manage-even if you just have one laptop.

The more devices you add, the more susceptible you are to attack.

Let us protect your network.



Our Cybersecurity Packages Include:
Why do we use
3rd party vendor management?
We’re committed to providing the strongest cybersecurity and IT management possible, something that no one person or company has the resources to do alone. Since we always put our customers first, we’ve partnered with other specialists to give you faster response times, better technology, and a higher level of support. Now we can give you national-level resources with local experience and care.












